Everything you need to know about VPNs before using

The term VPN is increasingly known among the world, since today, more and more people are concerned about their privacy and security when they surf the Internet. The large number of threats that circulate on the network, has made many users inform themselves of the way in which they can protect their data and identity while surfing the Internet, hence there are more and more people using this type of connections. Even so, there are still many that this term may sound like to Chinese, therefore, we will show what a VPN is, how it works, what it is for, advantages and disadvantages of using one and how we can navigate safely and privately both from the PC and from the mobile.
What is a VPN?
They are the initials of Virtual Private Network , or what is the same Virtual Private Network . Therefore, its name already gives us some clue as to what it is and what it is for. Specifically, it is a technology that allows us to connect our computer or any other device to a virtual private network using public as the Internet.
In other words, what a VPN does is to use a public network, usually the Internet, to create within this network a second virtual network in which the devices do not have to be physically connected and in which, using encryption techniques, It prevents data from being captured or accessible by other users of the network used as a base.
What is it for?
Initially, the use of VPNs was more oriented to the business world, however, there are many uses that we can give to such a tool.
Connect with work, or any other network, in a secure way : Through a VPN we can connect to our company’s network safely so as not to jeopardize the security of the company. This type of connection allows us to work as if we were in the company itself, since we will have access to all the information and resources.Surfing more securely : Today we use public Wi-Fi with total normality without thinking about the risks we run. In this case, the use of a VPN means that we are protected and that nobody who is connected to that network can access our private data.Increased privacy and camouflage our location : If we connect to the Internet through a VPN, the IP address of our device will be given to us by the server to which we connect. Therefore, that IP will have the same location as the server and not the actual location. In this way we can connect to services or access content with geographical restrictions.Skip certain restrictions of our provider : There are Internet providers that control user traffic, but if we use a VPN to surf the Internet, our provider will not be able to access the sites we visit since all the information will be encrypted or you will not know Nothing about our network activity.
Is it legal to use a VPN?
The answer to this question is a resounding yes , however, we must not confuse between the legality of the tool itself with the use or purposes with which we use a VPN.
As a computer tool they do not violate any laws, although it is true that some countries try to monitor their use or restrict them even though they are completely legal. Even in certain countries, it is the government that prohibits the use of certain VPNs , allowing only those approved by themselves. This is where the interests and the eagerness of the government of some countries, such as China, to have their citizens controlled come into play.
In this case, VPN providers have surely complied with certain requirements imposed by the government itself to avoid the complete privacy of users, as well as to avoid the use of certain services or access to censored content. In these cases, the government can impose very high fines on those who use tools not approved in their country. Luckily, none of this happens in our country and we can use this type of tools without any problem.
VPN types
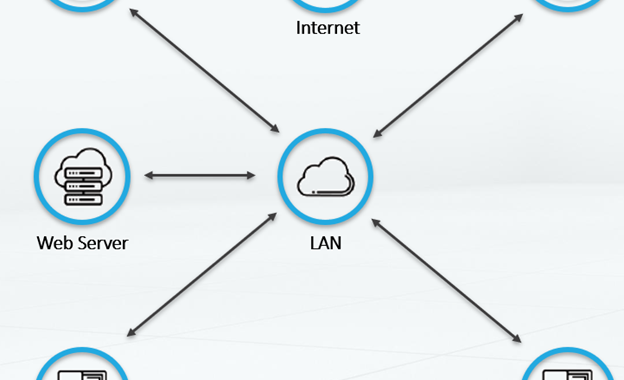
The truth is that VPNs can be classified according to the architecture used or the use scenario on the one hand and on the other hand, depending on the level of the TCP / IP model layer.
VPN remote access : It is the type that is used when we want to connect to our company’s network when we are out of it using the Internet as an access link. It is therefore a type of VPN used to protect the communications of individual computers with the internal network of an organization or company. The client computers must have installed and configured the software that allows the VPN connection and once identified, they will have an access level almost identical to the one that we have when we connect to the network of the company or organization locallyPoint-to-Point VPN : This type what it does is to protect the communications between two networks, of the same organization for example, that connect through the Internet. The protection it offers is for the connections between them, but it does not protect each of the networks internally.Tunneling : Basically, this technique is based on opening connections between two machines through a secure protocol (SSH for example) through which data transfers are made securely. This tunnel that is created between the interlocutors is only accessible to both, so that no one else can see the information that travels through it.VPN Over LAN: It is perhaps one of the least used, although at the enterprise level it is quite powerful. It is a variant of the remote access type, but instead of using the Internet as a means of connection, the company’s own local area network is used.